WiFi Security: Assessment of threats in wireless networks
08/03/2024Wifi connectivity has gone from being limited to restricted environments to becoming omnipresent in virtually every aspect of our daily lives. The ability to connect to the Internet from anywhere, be it at home, in a café, at work, in public spaces, or even in-flight, has enhanced the convenience in our daily lives. Moreover, the expansion of Wifi networks and the use of new manufacturing technologies now allow the interconnection of devices, leading to the significant rise of the Internet of Things (IoT) and providing users with more comprehensive control over their digital environments. However, this proliferation of Wifi networks has also given rise to new threats that require careful evaluation and effective security strategies to ensure secure and risk-free Wifi connections for our data and information. Common Wifi security threats include data interception Man-in-the-Middle (MITM) attacks One of the fundamental challenges in Wifi security is preventing MITM attacks, where an intruder inserts themselves into the communication between two parties, compromising the integrity and confidentiality of sensitive data such as passwords and financial information. Spoofing of access points Hackers can create fake Wifi networks that mimic legitimate ones to attract unsuspecting users. Once connected to these malicious networks, our data can be captured by cybercriminals who may sell or misuse it for illicit purposes. Tips for achieving a secure Wifi connection: Strengthen authentication and use security protocols Prioritize strong encryption for networks to protect confidential information transmitted through it. WPA (Wifi Protected Access) encryption uses stronger algorithms than its predecessor, WEP (Wired Equivalent Privacy), making it more difficult for hackers to intercept and decipher data. Advanced security protocols like WPA3 provide individualized data encryption and advanced two-factor authentication (2FA) methods, adding an extra layer of security by requiring additional verification. Device management Properly manage and monitor devices connected to Wifi networks to minimize risks associated with the large number of connected devices in homes and businesses. Regularly update the router firmware and all connected devices to address potential vulnerabilities. Segmentation of the network to separate critical devices from less secure ones also helps mitigate the risk of threat propagation. Secure Router Configuration The router secure configuration is what will ensure the robustness and overall security of a wireless network. The router, being the first point of contact for devices connected to the Internet, acts as the first line of defence against potential attacks. For this reason, it is important to understand that the proper configuration of the router not only guarantees a stable and efficient connection but also establishes a protected environment that safeguards the integrity and privacy of our data. How to configure the router securely? To ensure a correct and secure configuration of the router, it is recommended to: Change the default username and password of the router, as these are easily accessible to attackers. Use strong passwords containing a combination of letters, numbers, and special characters. Disable remote administration to prevent cybercriminals from accessing the router externally. Enable WPA2 or WPA3 encryption instead of the outdated WEP for enhanced network security. Optionally, disable SSID broadcast to make the network less visible and harder to detect by hackers. Keep the router firmware updated to address vulnerabilities and improve overall device security. By following these steps, you will strengthen the security of your wireless network and reduce the chances of experiencing unwanted attacks or intrusions.
[ ... ]Xiaomi
XiaomiIn little more than 10 years, the Chinese multinational Xiaomi has become a giant in the electronics industry. It is a really impressive trajectory if we take into account that in this short period of time it has put itself on a par with companies like Apple, Samsung or Huawei. Xiaomi, has realized that the world is a big market, and it does not stop expanding. It is now an Internet company with smartphones and smart hardware connected by an Internet of Things (IoT) platform at its core. Its sales are growing steadily and it continues an unstoppable race to innovate and achieve a high-quality user experience and operational efficiency.
[ ... ]
Cookies
A cookie is a file that is downloaded to your computer to access certain web pages. Cookies allow a website, among other things, to store and retrieve information about the browsing habits of a user or their equipment and, depending on the information they contain and how you use your computer, they can be used to recognize the user. However, this only means obtaining information related to the number of pages visited, the city assigned the IP address from which you accessed, the number of new users, frequency and recurrence of visits, time of visit, the browser or the operator or terminal type from which the visit takes place. In no event will data be obtained about the full name or address from which the user is connected. The cookies used on this website and the specific purpose of each one are: UTMA Cookie: We use this cookie to count how many times a unique user visits the site. UTMB Cookie: We use this cookie to calculate how long a user stays on a page. UTMZ Cookie: This cookie stores the visitor's origin, the path followed to access the web, either the direct access from a link on another website, from an email link using certain keywords in a search engine, through a display campaign, or through an AdWords ad. UTMC Cookie: The current JavaScript code that Google Analytics uses does not require this cookie. This cookie is used, along with the utmb cookie, to determine if after more than 30 minutes on the same page a new session should or should not be established for the user. This cookie is still written to ensure compatibility with the websites where you installed the old urchin.js tracking code. PHPSESSID Cookie: We use this cookie to identify the relevant user. You can allow, block or delete cookies installed on your computer by setting your browser options. You can find information about how, in relation to the most common browsers, on the links listed below: Explorer: http://windows.microsoft.com/es-es/windows7/how-to-manage-cookies-in-internet-explorer-9 Firefox: http://support.mozilla.org/es/products/firefox/cookies Chrome: http://support.google.com/chrome/bin/answer.py?hl=es&answer=95647 Safari: http://support.apple.com/kb/ph5042 Please note, however, that there is the possibility that disabling any cookie may prevent or hinder navigation or the provision of services offered on this website.
[ ... ]OPPO joins the Connectivity Standards Alliance
21/10/2021Oppo has announced its membership on the Board of Directors of the Connectivity Standards Alliance (CSA), the organization with more than 400 technology companies working together to increase compatibility in IoT through simpler technology standards. One of Oppo's main objectives in his new role, explained Neil Yang, director of OPPO's Standards Research Department, is to promote Matter, the base protocol for the Internet of Things (IoT), offering a simplified user experience that allows connecting different devices "We want to create a highly compliant IoT ecosystem, and drive the development of the Alliance's advancements together with other partners through proposals for new protocols, setting new standards and developing new Matter-based products”, says Yang. For the CSA, Oppo's commitment is an open door to promote Matter in China and throughout Asia, offering the possibility of providing better IoT experiences to more than one billion users.
[ ... ]How to keep your Mac safe?
28/06/20215 things you should do to protect your Mac How many times have we heard that Mac is a more than secure and unbreakable system? For years, Apple has made its security through obscurity, or in other words, its proprietary software, flagship and brand guarantee. Today, however, just when Mac is no longer a minority option, Steve Jobs' system has become another favorite target for hackers and cybercriminals. The market has responded to this with the development of specific protection tools for Mac, while Apple works on optimizing its system in each version. Knowing what kind of tools exist for Mac and which ones are already included in our computer will help us to stay safe and choose the best strategy that fits our needs and use of the equipment. 1. Use computer security tools Cybersecurity is a universal and necessary practice in all operating systems today. The objective is to ensure protection against attacks and theft by cybercriminals who are looking for personal or confidential information stored on our computers or that enters or leaves them, in order to use it for their own benefit. What is VPN security? Cybersecurity tools help us to minimize our footprint on the Internet and thus increase our privacy and security. In this regard, VPN services for Mac stand out, as they incorporate advanced protection technologies capable of connecting to the Internet through intermediate servers, so that our IP address - our identification on the network - is replaced by the IP address of this secure server, without anyone being able to trace our connection. This type of VPN service also encrypts any information leaving our computer, thus preventing it from being accessed on its journey to its destination. This is essential, for example, when using public Wi-Fi networks to connect to the Internet. 2. Keep the operating system and software up to date As simple as it may seem, one of the best and easiest ways to protect a Mac is to always have the latest version of the operating system installed and to work with updated software downloaded from the Mac App Store. System updates usually include security patches, among other things. How do I update my Mac? Through the System Preferences Panel of our computer we can set that when there are available updates we receive a notice from MacOs warning us of it or that these updates, whether system data files, security updates or official software are installed automatically. To check if we are working with the latest versions available and our Mac is up to date we can do it by checking through this same panel if there are updates available at that time. If we have checked the automatic updates option, Mac will do this task for us routinely. 3. Use secure settings Mac's default security settings can be greatly enhanced by manually configuring the security and privacy terms of our computer. How to change the Privacy and Security preferences on the Mac? By accessing the "Privacy" tab of the "Security and Privacy" option of the Control Panel we will have the option to manage what information we allow our computer to make available to others over the Internet or on a network and what applications we allow access to our data and files. In the same way, but through the "Security" tab, we will be able to incorporate passwords for the access to different tasks and operations of the computer and through the "FileVault" tool we will be able to ensure the encryption, for example, of our personal information or certain documents for which a password will be required to unblock them. 4. Use an Antivirus for Mac There are antivirus programs developed specifically for Mac. Some of them are special for certain threats, although in general most of them offer a wide range of services to help us keep our computers safe. Which is the best antivirus for Mac? The range of antivirus for Mac, free and paid, is nowadays much wider than a few years ago, highlighting among the most complete and advanced, antivirus with malware protection functions in real time, tools against digital identity theft, protection against spyware or advanced detection and removal of blackmail programs. 5. Make regular backups Apple has a native function, Time Machine, which makes backup copies of our hard disk on a separate secondary disk, so that if for any reason we suffer an attack or a breakdown we can recover all the information. Many antiviruses offer a backup service, backup or backup similar but in the cloud, as a preventive measure against writing errors on the disk, theft of devices or even against data hijacking or ransomware.
[ ... ]What can I do if my computer runs very slow?
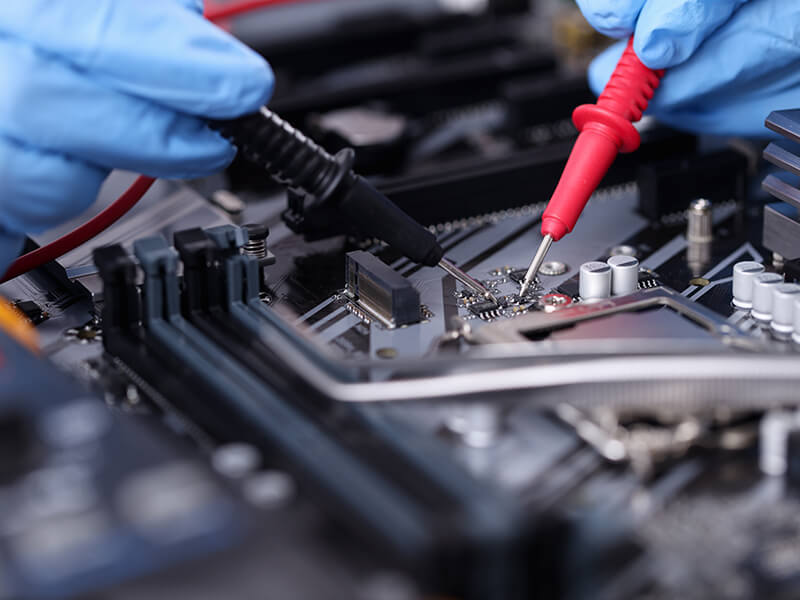
22/05/2021If your computer is running slow, do not despair. The use of a computer like any other machine needs proper maintenance and the performance of our PC can be severely affected by the lack of attention to this task. But, don't worry, if you want your computer to work as it did on the first day, we explain how to get it back. Why is my computer so slow? Computer slowness can be due to hardware, software, connectivity and even tidiness and cleanliness problems! Every computer needs a minimum maintenance so these failures can be avoided and only if we pay this kind of attention we can ensure an always-optimal performance for our computer, prolong its life and work or enjoy our PC, without despairing. I have tried everything, but my computer is still very slow. What can I do? If your computer is slow and you have already tried the typical things like closing secondary tasks, disabling the automatic execution of programs, you have verified that you have free space on the hard disk and restarted the PC, and everything is still the same, it is clear that something is wrong with your machine and you should consider resorting to a professional computer repair service, so that they can fix it. You can search a thousand videos on the Internet, but... do you really know why your computer is slow? Why does your computer start up very slowly? Or why has your computer become slow after a while of working with it? Are you sure that what you want to do will not end up causing another error or, even worse, another more serious problem? Is it necessary to go to a professional Computer Repair Service to fix the slow computer problem? The answer is yes, if what we are looking for is to really fix the problem and prevent it from happening again. You can save a lot of time and money by using a professional computer repair service. The best computer repair services work with specialized technicians who have the necessary knowledge to make a quick and accurate diagnosis that will allow you to give your computer a new lease of life. In addition, professional computer repair services have the right tools and all the licensed software to be able to intervene. What will a Computer Repair Service do to speed up my slow PC? The first and foremost thing that a professional computer maintenance service can offer you is a maintenance plan for your computer, tailored to your needs. With this alone, you will most likely avoid many problems related to the performance of your machine, including speed problems, right from the start. They will be able to, among other things, repair or replace any part of your computer causing any problem, they will perform a deep search for viruses to eliminate them; and if necessary, they can clean the cooling system of your computer to remove internal dust, one of the most common causes of slow computer performance - dust accumulated in the internal fans can reduce their efficiency and cause overheating of the machine and its mechanical components -. Sometimes we think about replacing the machine when a simple repair and a good maintenance can bring our PC back to life. When was the last time you had your computer serviced?
[ ... ]